The Evolution of Clawdbot Malware: From Early Variants to 2026
Tracing the Growth of Clawdbot Attacks and Modern Defense Strategies
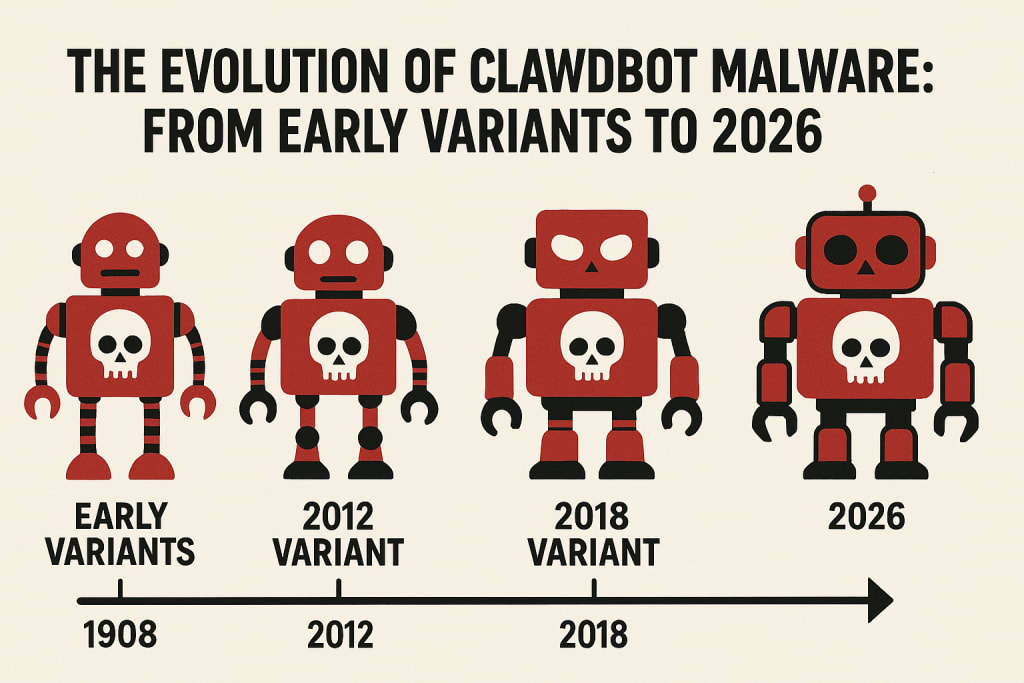
Malware continues to be one of the most persistent threats in the digital landscape, constantly adapting to evade detection and exploit emerging vulnerabilities. Among these, Clawdbot malware has become notorious for its sophistication and resilience. Since its initial appearance, Clawdbot has evolved considerably — from a relatively simple bot to a multifaceted cyber threat capable of data theft, lateral movement, and stealthy persistence. Understanding its evolution is critical for organizations looking to protect their networks and fix Clawdbot security risks before damage occurs.
Origins of Clawdbot: Humble Beginnings
Clawdbot first emerged in the early 2020s as a rudimentary botnet agent designed to target poorly protected servers and consumer devices. Its earliest variants focused on brute force attacks against exposed SSH services, automatically scanning IP ranges and attempting default or weak credentials. While limited in capability, these initial versions were successful enough to amass a large network of infected devices, giving researchers their first glimpse of what would become a persistent threat.
These early versions were primarily coded to:
- Harvest credentials
- Launch distributed denial of service (DDoS) attacks
- Provide remote shell access to attackers
At this stage, traditional signature-based antivirus tools could detect most Clawdbot variants fairly reliably.
Sophistication Through Self-Modification
By 2022–2023, Clawdbot evolved into a more sophisticated threat. Developers began incorporating self-modifying code to evade detection and implemented encryption routines to disguise communication with command-and-control (C2) servers. This shift marked a notable milestone in its evolution: Clawdbot was no longer just a brute-force device; it had become a stealthy infiltration tool.
Key advances during this period included:
- Encrypted C2 communications to avoid network-based detection
- Modular payloads, enabling the malware to download additional capabilities dynamically
- Persistence mechanisms that survived reboots and basic remediation attempts
Organizations struggling to defend against these variants realized they needed proactive strategies — including threat hunting and behavioral analysis — to fix Clawdbot security risks rather than simply deleting infected files.
Targeted Campaigns and Expanded Objectives
By 2024, Clawdbot had transformed from a generic bot into a more targeted threat. Threat actors began tailoring attacks against specific industries, particularly healthcare, manufacturing, and finance. Instead of random scanning, newer variants used reconnaissance tools to identify high-value targets and avoid low-impact systems.
At this stage, Clawdbot evolved to include:
- Credential dumping
- File exfiltration capabilities
- Lateral movement through internal networks
- Polymorphic components that changed structure with each infection
These developments made Clawdbot a serious enterprise-level threat. Detecting and mitigating it required coordinated incident response efforts, with emphasis on network segmentation, multi-factor authentication, and regular patch management.
Clawdbot in 2025–2026: AI-Driven and Highly Resilient
In the current landscape of 2026, Clawdbot has advanced yet again integrating artificial intelligence elements to make attacks more adaptive and harder to predict. Modern variants use machine learning models to analyze network configurations, choose optimal exploitation paths, and adjust their behavior based on defensive countermeasures.
This cutting-edge evolution includes:
- AI-assisted decision making, improving infiltration efficiency
- Zero-day exploitation routines, capable of identifying and leveraging previously unknown vulnerabilities
- Encrypted peer-to-peer C2 models, reducing dependency on fixed servers
- Stealthy data exfiltration techniques that mimic normal traffic
Given this level of sophistication, organizations cannot rely solely on traditional defenses to fix Clawdbot security risks. Solutions such as zero-trust architecture, extended detection and response and security-orchestration automation become essential.
Conclusion
From a basic brute-force bot to an AI-infused enterprise threat, the evolution of Clawdbot malware illustrates the shifting landscape of cyber risk. In 2026, defending against such dynamic threats demands adaptive security strategies and a commitment to ongoing vigilance. By combining modern defensive tech with best practices, organizations can better fix Clawdbot security risks and stay ahead of emerging threats.
About the Creator
Timesofai
Timesofai brings you global information regarding artificial intelligence, whether it is related to an innovation with AI or an AI tool taking over the world. For every small update in AI industry, you can visit https://www.timesofai.com/






Comments
There are no comments for this story
Be the first to respond and start the conversation.