What Are the Key Components of a Smart Contract?
Key Elements That Ensure Accuracy, Security, and Execution on the Blockchain

Smart contracts are often described as self-executing digital agreements, but this definition only scratches the surface. In practice, a smart contract is a carefully engineered system composed of multiple interdependent components, each playing a critical role in ensuring correctness, security, and reliability. When any one of these components is poorly designed or misunderstood, the entire contract can fail sometimes with irreversible consequences.
As smart contracts increasingly underpin financial systems, digital ownership, and decentralized governance, understanding their core components is no longer just a developer concern. It is essential knowledge for founders, auditors, investors, and anyone evaluating the trustworthiness of on-chain systems. This article provides a deep, structured exploration of the key components of a smart contract, explaining not just what they are, but why they matter and how they interact in real-world deployments.
Smart Contracts as Programmable Systems, Not Just Code
Before breaking down individual components, it is important to reframe how smart contracts are viewed. They are not merely snippets of code deployed on a blockchain; they are programmable systems operating in adversarial, public environments. Unlike traditional software, smart contracts:
Cannot be easily patched after deployment
Manage real economic value
Are executed by decentralized networks rather than private servers
This context elevates the importance of each component. Design decisions that might be acceptable in Web2 software such as vague assumptions or deferred error handling can become critical vulnerabilities in smart contracts.
Contract Logic: The Core Rules of Execution
At the heart of every smart contract lies its business logic. This is the component that defines what the contract does: how it responds to inputs, how state changes occur, and under what conditions actions are triggered.
Contract logic translates real-world agreements into deterministic rules. For example, in a lending contract, logic defines how interest accrues, when collateral can be liquidated, and who is allowed to borrow or repay. Precision is essential, because ambiguity common in legal contracts is not tolerated in code.
Well-designed logic is:
Explicit rather than implicit
Deterministic rather than conditional on external interpretation
Minimal rather than feature-heavy
Many high-profile failures in Web3 stem from logical flaws rather than syntax errors, underscoring how critical this component is.
State Variables and On-Chain Storage
Smart contracts maintain state, which represents the contract’s memory of past interactions. State variables store information such as balances, ownership records, configuration parameters, or governance outcomes.
Because state is stored on-chain, it is persistent, transparent, and expensive to modify. Poor state design can lead to inefficiencies, security risks, or even permanent corruption of contract behavior. For example, incorrectly ordered storage variables can cause severe issues in upgradeable contracts, while overly complex state structures increase gas costs and attack surface.
Effective state management focuses on:
Storing only what is necessary
Protecting critical state from unauthorized modification
Anticipating how state will evolve over time
State is not just data it is the backbone of contract reliability.
Functions and External Interfaces
Functions define how users and other contracts interact with a smart contract. They form the public and internal interfaces through which logic is accessed and executed.
Public and external functions are particularly sensitive, as they represent entry points for both legitimate users and attackers. Each function must clearly specify:
Who is allowed to call it
What inputs are accepted
What state changes may occur
Internal functions, while less exposed, still contribute to overall safety by organizing logic and reducing duplication. Clear, well-structured function design improves auditability and reduces the likelihood of overlooked edge cases.
Access Control and Permission Models
Access control is one of the most critical components of any smart contract. It defines who can do what, and under which conditions. Weak access control has been responsible for some of the most damaging exploits in blockchain history.
Effective permission models go beyond a single “owner” address. They may include:
Role-based permissions
Time-locked administrative actions
Multi-signature or governance-controlled privileges
From a systems perspective, access control is about minimizing trust. The fewer assumptions a contract makes about human behavior, the more robust it becomes in the long term.
Events and Transparency Mechanisms
Events are often overlooked, but they play a vital role in smart contract ecosystems. Events emit structured logs that allow off-chain systems such as user interfaces, analytics platforms, and monitoring tools to track contract activity.
While events do not affect on-chain state, they significantly improve transparency and usability. Well-designed events:
Provide clear insight into contract behavior
Enable real-time monitoring and alerts
Support compliance and forensic analysis
In complex systems, events serve as the contract’s public narrative, explaining what happened and when.
External Dependencies and Oracles
Many smart contracts depend on data or functionality outside the blockchain. This may include price feeds, randomness, identity verification, or cross-chain communication. These external dependencies are typically accessed through oracles or other intermediary contracts.
External dependencies are among the highest-risk components of a smart contract. If the data source is compromised or manipulated, the contract may behave exactly as coded but in a way that is economically disastrous.
Robust contracts:
Minimize reliance on external inputs
Use multiple data sources where possible
Define fallback behavior for oracle failure
Understanding how a contract interacts with the outside world is essential to assessing its true risk profile.
Error Handling and Fail-Safe Mechanisms
In traditional software, errors can often be patched or worked around. In smart contracts, errors must be anticipated and handled at design time.
Fail-safe mechanisms include:
Input validation and explicit revert conditions
Circuit breakers or pause functions
Conservative assumptions about execution order
These mechanisms do not make contracts infallible, but they can significantly limit damage when something goes wrong. A contract that fails safely preserves trust far better than one that fails silently or catastrophically.
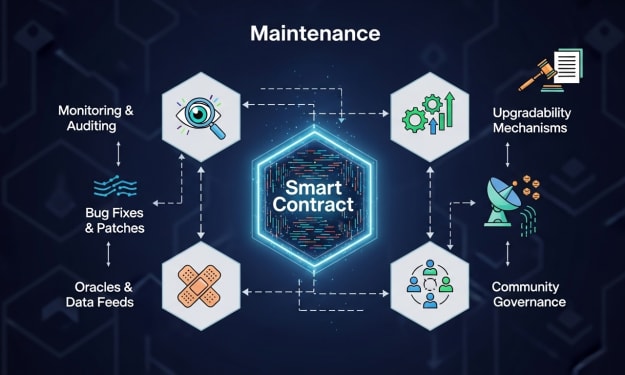
Upgradeability and Lifecycle Planning
Immutability is a defining feature of smart contracts, but many systems still require evolution. This introduces the component of upgradeability, which must be designed explicitly rather than retrofitted.
Upgrade mechanisms involve:
Proxy patterns separating logic and storage
Governance or admin controls over upgrades
Careful management of storage layout
Upgradeability adds flexibility but also introduces risk. Each upgrade path becomes a potential attack vector, making rigorous testing and documentation essential.
Security Assumptions and Invariants
Every smart contract is built on a set of assumptions—about users, markets, and execution environments. Secure contracts make these assumptions explicit and enforce invariants, conditions that must always remain true.
Examples include:
Total supply consistency
Conservation of value
Non-negativity of balances
Invariants act as internal guardrails. When they are violated, it signals a fundamental problem. Many advanced testing and auditing approaches focus on identifying and validating these invariants across all execution paths.
The Role of Auditing in Validating Components
Because smart contracts combine multiple complex components, independent review is essential. Smart Contract Auditing evaluates how these components interact, identifying weaknesses that may not be obvious in isolation. A comprehensive Smart Contract Audit examines logic, state management, access control, and external dependencies as a unified system. For high-stakes deployments, engaging a specialized Smart Contract Audit Company is often the final checkpoint before trust is extended to autonomous code.
Auditing does not replace good design, but it provides an external lens that significantly improves confidence.
Real-World Lessons From Component Failures
Looking at past incidents reveals a consistent pattern: failures rarely occur because developers misunderstood syntax. Instead, they arise from overlooked interactions between components such as logic that assumed oracle reliability, or access control that failed under upgrade scenarios.
These lessons reinforce a core truth: smart contracts must be understood holistically. Each component influences the others, and weaknesses compound rather than cancel out.
Conclusion
A smart contract is only as strong as the system of components that define it. Contract logic, state management, access control, external dependencies, and lifecycle planning all contribute to whether a contract can be trusted to operate safely and predictably.
As smart contracts continue to move from experimental tools to foundational digital infrastructure, understanding their key components becomes a prerequisite for responsible participation in Web3. Those who take the time to design, review, and understand these components thoroughly are not just writing better code they are building systems worthy of trust in a decentralized world.
About the Creator
Dominic34
I specialize in helping blockchain startups and crypto projects launch, grow, and scale through strategic token development, decentralized fundraising guidance, and Web3-focused marketing.





Comments
There are no comments for this story
Be the first to respond and start the conversation.